Digital identity is no longer just an IT tech team topic. At this year’s Gartner Identity & Access Management Summit in London (March 9 – 10), it was clear that identity security is becoming a board-level priority, driven by rising cyber threats, regulatory pressure, and the growing importance of technological sovereignty.
As organizations increasingly evaluate where their critical infrastructure comes from and who controls it, the importance of European-owned technologies is growing. At Evolveum, we brought this discussion to our booth, as midPoint is exactly where EU sovereignty meets open source IGA. That is what midPoint has always been and always will be: a complete open source IGA platform. Not only is it recognized by Gartner as such and developed and owned in Europe, it provides freedom across many dimensions.

Live midPoint demos driven by real questions
At our booth, Evolveum’s Head of Engineering Slávek Licehammer offered midPoint demonstrations with a twist: instead of having a pre-recorded video, he invited visitors to ask what they wanted to see and demonstrated midPoint live based on their requests. This format led to highly practical discussions focused on real-world identity governance and administration challenges.
One of the capabilities that attracted significant interest was the Simulations feature. This functionality allows organizations to evaluate the impact of configuration changes on real data before implementing them, helping teams make informed decisions without risking disruptions to production environments. From a business perspective, this means reducing operational risk, preventing costly configuration errors, and improving data quality without slowing down innovation.
Another major topic at our booth was rapid application onboarding, one of the most persistent challenges in IGA programs. Pavol Mederly, Evolveum’s Chief Product Officer, demonstrated midPilot, midPoint’s AI-powered assistant designed to accelerate application onboarding and improve visibility across identity ecosystems.

Rethinking application onboarding with AI
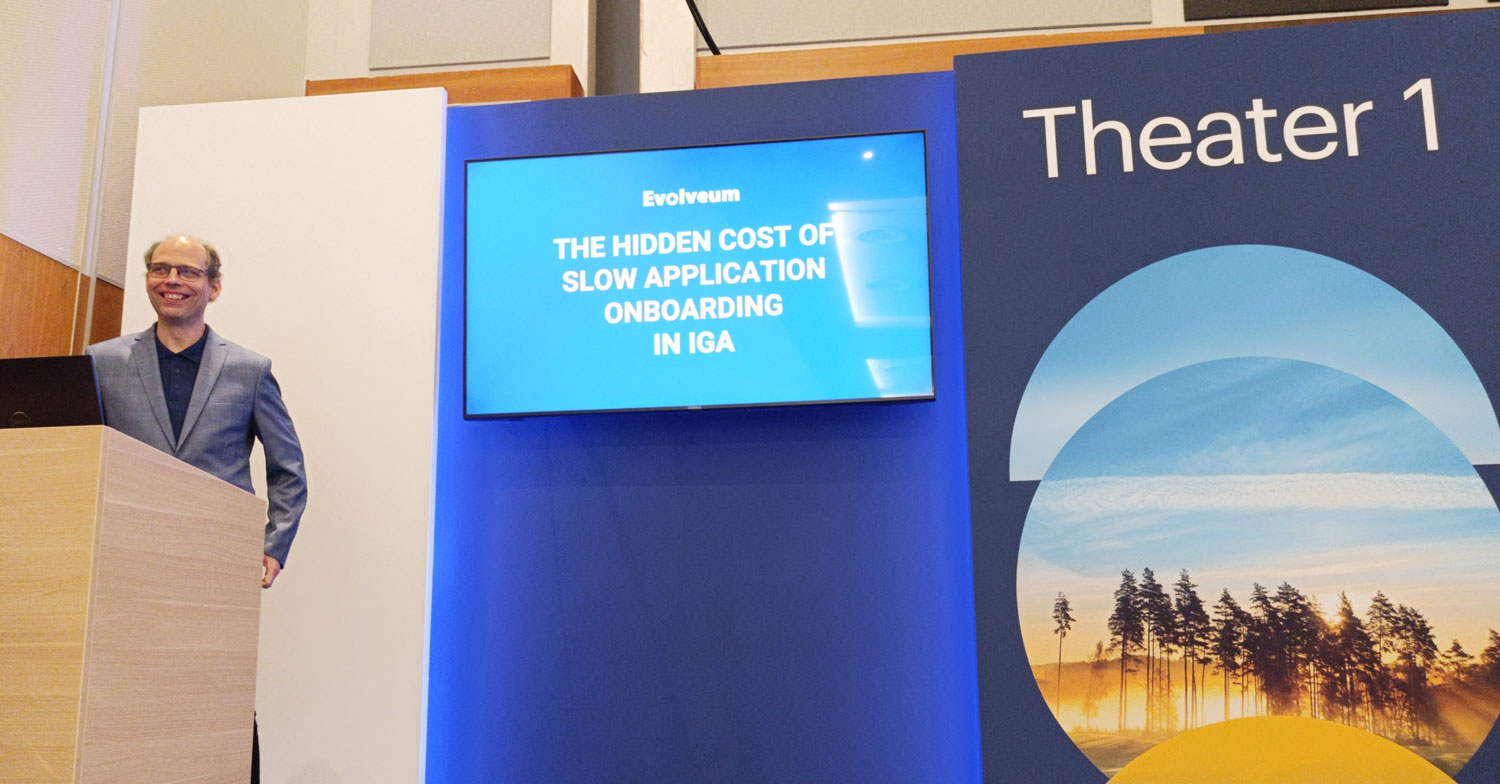
Today, roughly 80% of cyberattacks exploit identity-related vulnerabilities, and one of the biggest contributing factors is incomplete application integration. When applications are not properly governed, they create security blind spots. Interest in this topic was clearly reflected in Pavol Mederly’s theater session on day two, titled The hidden cost of slow application onboarding in IGA.
The session focused on common but often underestimated problems:
- 1. Highly skilled engineers spending large amounts of time building and maintaining integrations instead of delivering strategic value.
- 2. The risk of low visibility across numerous connected systems.
The presentation showed how midPilot – the integral AI part of midPoint – addresses these challenges with a no/low-code approach combined with AI assistance, and significantly reduces this burden.
The strong attendance of Pavol’s theater session confirmed that this challenge remains one of the most relevant operational issues in IGA programs today.

Community, conversations, and a bit of fun
During the summit, we had many valuable conversations with C-level people, architects, security leaders, and IGA practitioners facing similar challenges across industries. Beyond technological discussions, we added a bit of fun to the experience. Visitors could participate in our raffle for a Lord of the Rings Sauron LEGO set by playing memePoint, our identity-themed meme matching game where participants paired funny captions with equally funny images to create the best combination. It turned out to be a great conversation starter and a reminder that even in a serious field like cybersecurity, creativity and community matter.

Looking ahead
Events like the Gartner IAM Summit confirm what we see across the industry: identity management and governance is becoming more strategic, more complex, and more central to organizational security. Digital sovereignty is becoming a must.
At the same time, organizations are looking for solutions that are not only powerful, but also transparent, flexible, and future-proof. This is exactly where the combination of open source and strong identity governance and administration capabilities continues to stand out.
We are grateful to everyone who stopped by our booth, joined our session, or shared their identity challenges with us. We look forward to continuing these conversations and seeing how the identity community continues to evolve: feel free to join us at the next event from May 12-15 in Prague – the 2nd Annual MidPoint Community Meetup.
This project has received funding from the European Union through the Recovery and Resilience Plan of the Slovak Republic.

